Labyrinth Deception Platform v2.0.51: Release notes Release

02.11.2023
Cisco acquires Splunk, but how do you convince Splunk customers that Cisco has advantages
01.11.2023
CrowdStrike provides 100% coverage according to the MITRE Engenuity ATT&CK® Evaluations: round 5
31.10.2023
Top 20 Shocking Data Breach Statistics for 2023
06.09.2023
Adversaries Can “Log In with Microsoft” through the nOAuth Azure Active Directory Vulnerability
06.09.2023
iIT Distribution is the official distributor of LogRhythm!
31.08.2023
Instant replication with NAKIVO Backup & Replication v10.10 Beta
03.08.2023
Effective communication: Email vs. Instant Messaging?
25.07.2023
Infinidat Expands Support for Hybrid Cloud Storage Deployments with InfuzeOS Cloud Edition
14.07.2023
Falcon Insight for ChromeOS: The Industry’s First Native XDR Offering for ChromeOS
03.06.2023
Opening new horizons: iIT Distribution is the official distributor of Gatewatcher
13.05.2023
Another revolution in cybersecurity from CrowdStrike: top 5 important things to know about Managed XDR (MXDR)
09.05.2023
GTB Technologies is the best solution in the DLP industry
04.04.2023
CrowdStrike Falcon Platform Detects and Prevents Active Intrusion Campaign Targeting 3CXDesktopApp Customers
24.03.2023
Labyrinth Deception Platform v2.0.51: Release notes
23.03.2023
SIEM vs Log Management Systems: What you need to know before choosing
15.03.2023
CrowdStrike Falcon Named the Winner of the 2022 AV-TEST Award for Best MacOS Security Product
10.03.2023
CrowdStrike 2023 Global Threat Report: Resilient Businesses Fight Relentless Adversaries
10.03.2023
Threema Work App Update: Encrypted Group Calls Are Now Available on Android Devices
28.02.2023
CrowdStrike Ranked #1 in the IDC Worldwide Endpoint Security Market Shares Report for Third Time in a Row
21.02.2023
Picus Red Report 2023: The Top 10 Most Prevalent MITRE ATT&CK Techniques Used by Attackers
14.02.2023
On leadership in the sphere of high-end unified storage: An exclusive interview with Phil Bullinger, CEO of Infinidat
11.02.2023
Securing PostgreSQL from Cryptojacking Campaigns in Kubernetes
30.01.2023
What's New in NAKIVO Backup & Replication v10.8: Release Overview
16.01.2023
Success Story: Georgian Bank Achieves 100% Backup Success Rate with NAKIVO
12.01.2023
CrowdStrike Named a Leader in Frost & Sullivan’s 2022 Frost Radar for Cyber Threat Intelligence
12.12.2022
DDoS Attack Prevention and DDoS Protection Best Practices
21.11.2022
How Hackers Can Bypass Multi-Factor Authentication
08.11.2022
CrowdStrike Achieves Red Hat OpenShift Certification: Streamlining Visibility and Automating Protection for OpenShift
03.11.2022
Infinidat Recognized as a Leader in Gartner Magic Quadrant for Primary Storage – 5th Year in a Row
19.10.2022
New version of NetBrain Release 11: the key to reducing the cost of NetOps
13.10.2022
With security revenue surging, CrowdStrike wants to be a broader enterprise IT player
05.10.2022
CrowdStrike Announced the Acquisition of Reposify to Bolster Visibility and Reduce Risk Exposure of External Assets
22.09.2022
Kubernetes против Docker: в чем между ними разница?
16.09.2022
Infinidat расширяет функции NVMe/TCP для сред VMware
15.09.2022
Новые возможности InfiniBox от Infinidat: vVols репликация для VMware сред
02.09.2022
Индикаторы атак на основе искусственного интеллекта позволяют максимально быстро прогнозировать и останавливать угрозы
03.08.2022
Истории с Dark Web: Отслеживание подпольной экономики eCrime улучшает эффективность киберзащиты
22.07.2022
Развитие ботнетов и DDoS-атак
15.07.2022
Lookout обнаружила шпионское ПО для Android, развернутое в Казахстане
11.07.2022
Выявление и смягчение атак NTLM-ретрансляции, нацеленных на контроллеры домена Microsoft
20.06.2022
Что такое демократизация данных?
07.06.2022
Неизменные резервные копии: что вам нужно знать, чтобы защитить свои данные
22.05.2022
Украинские Киберактивисты Использовали Скомпрометированные Docker Honeypots Для Антироссийских Dos-Атак
06.05.2022
ЧТО НОВОГО В LABYRINTH DECEPTION PLATFORM: РЕЛИЗ 2.0.32
22.04.2022
PALO ALTO NETWORKS проинформировала об уязвимостях, которые могут разрешить злоумышленникам отключить платформу CORTEX XDR
15.04.2022
INSPUR ВТОРОЙ ГОД ПОДРЯД СТАНОВИТСЯ ОБРАЗЦОВЫМ ПОСТАВЩИКОМ CLOUD-OPTIMIZED ОБОРУДОВАНИЯ ПО ВЕРСИИ GARTNER HYPE CYCLE
08.10.2020
Intelligent IT Distribution взяла участь у Третьому щорічному Міжнародному Форумі «Кібербезпека - Захистимо Бізнес, Захистимо Держава»
29.09.2020
iITD - партнер форуму “Кібербезпека - захистимо бізнес, захистимо державу” 2020
24.09.2020
Компанія IIT Distribution отримала статус дистриб’ютора рішень NetBrain Technologies на території України
28.08.2020
Fal.Con 2020 від CrowdStrike
25.08.2020
Дотримання норм страхування кіберризиків
25.08.2020
Автоматично блокуйте скомпрометовані облікові записи з Lepide Active Directory Self Service 20.1
25.08.2020
Компанія Cossack Labs запрошує відвідати NoNameCon
22.07.2020
Підписання дистриб’юторської угоди з компанією Safe-T
21.07.2020
Міжнародна конференція: "Online Banking - Час інновацій!"
18.06.2020
Глобальний звіт про кіберзагрози 2020
11.06.2020
Четвер, 25 червня 2020 року. Не пропустіть!
05.05.2020
Анонс: нова версія Acra Enterprise забезпечує підвищену гнучкість для високонавантажених систем
13.04.2020
Lepide Remote Worker Monitoring Pack - легка платформа безпеки, яка гарантує негайний захист даних бізнесу протягом непередбаченого періоду віддаленої роботи.
12.04.2020
Забезпечення кібербезпеки для віддалених користувачів
08.04.2020
Labyrinth Technologies пропонує скористатися спеціальною пропозицією - ліцензія на 12 місяців за ціною 6 місяців.
07.04.2020
«CrowdStrike: дистанційна робота та ІТ-безпеку за часів кризи - скорочена ліцензійна програма на 3-6 місяців».
23.03.2020
Компанія iIT Distribution отримала статус дистриб’ютора рішень RedSeal Networks на території України.
23.03.2020
Компанія iIT Distribution отримала статус дистриб’ютора рішень Lepide на території України.
16.03.2020
Компанія iIT Distribution починає дистрибуцію рішень CrowdStrike на території України.
19.02.2020
20 лютого у Києві відбудеться щорічна конференція CISO DX DAY 2020
18.02.2020
Компанія iIT Distribution отримала статус дистриб’ютора рішень Instana на території України.
17.02.2020
Exabeam Security Intelligence Platform допомагає
A new version of Labyrinth, a highly effective solution for detecting and stopping hacker activity inside corporate networks, has recently been released. This update offers a number of new and improved features, as well as important fixes, which we will discuss in detail in this article.
1. NEW AND IMPROVED
1.1. Integrations: CrowdStrike
The integration allows you to:
- Enrich the alert with data about the host from which the attack was launched based on the alert's Source IP;
- Isolate the host if it has a Crowdstrike agent, and this host is the source of the alert; Network containment (optional).

1.2. Integrations: Fortigate
Labyrinth Deception Platform integrates with available Fortigate devices for:
- Enriching alerts with data about the attacking host;
- Implementing a mechanism to isolate a host in the network if it is involved in a security incident, i.e., if it has been observed performing malicious actions on Point.

1.3. New Point types for SCADA/OT protection
To protect SCADA/OT, new Point types have been developed that can emulate Web interfaces PLC, Siemens S7COMM, SNMP, Modbus, etc.
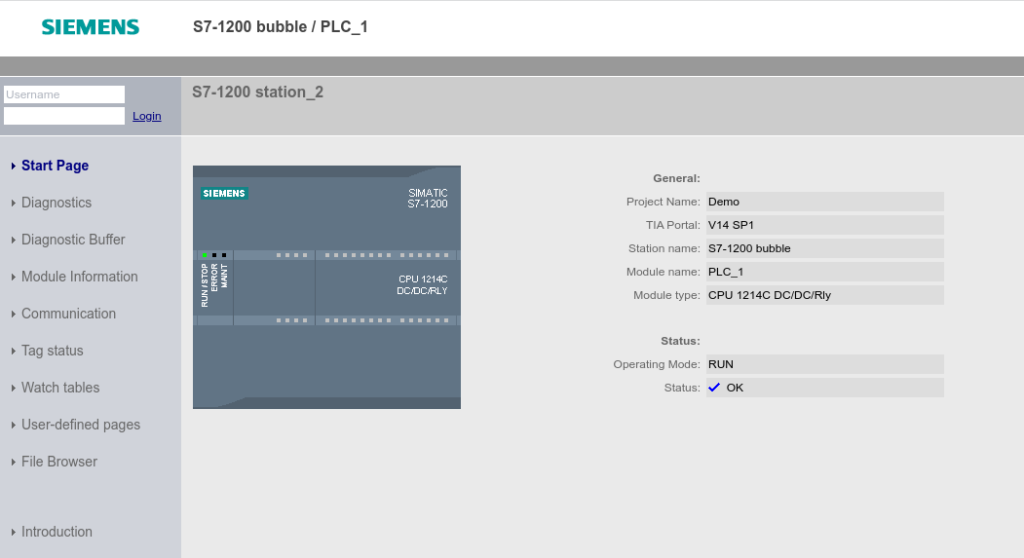
1.3.1. Siemens Simatic S7-1200
This Point type emulates PLC Siemens Simatic S7-1200, namely:
- web interface;
- S7COMM protocol for communication with PLC;
- SNMP.


1.3.2. Siemens Simatic S7-300 and S7-1500
Like the previous Point type, S7-300 and S7-1500 emulate S7COMM, SNMP but without a web interface. However, the alerting and overall performance of SNMP and S7COMM are identical to S7-1200.
1.3.3. Rockwell Allen Bradley PLC та Ethernet Processor SLC-500
Also, web interface simulations were added for Rockwell Allen Bradley:
- Allen Bradley PLC CompactLogix 5069-L320ER/A
- Allen Bradley Ethernet Processor SLC-500 (1747-L552/C)

1.3.4. Modbus TCP Server
Modbus TCP Server is a type of Point that uses TCP/IP networks for communication. If it is present in the Honeynet settings, it is possible to detect any interaction with the Point via the Modbus TCP protocol: an attempt to read and write registers, an attempt to get a description of the server, etc.


1.3.5. MQTT Broker imitation
MQTT is not directly related to SCADA, but rather to the IoT topic. MQTT Broker is a Point type, which is a full-fledged MQTT broker and allows you to publish notifications to the topics, subscribe to the topics, etc.


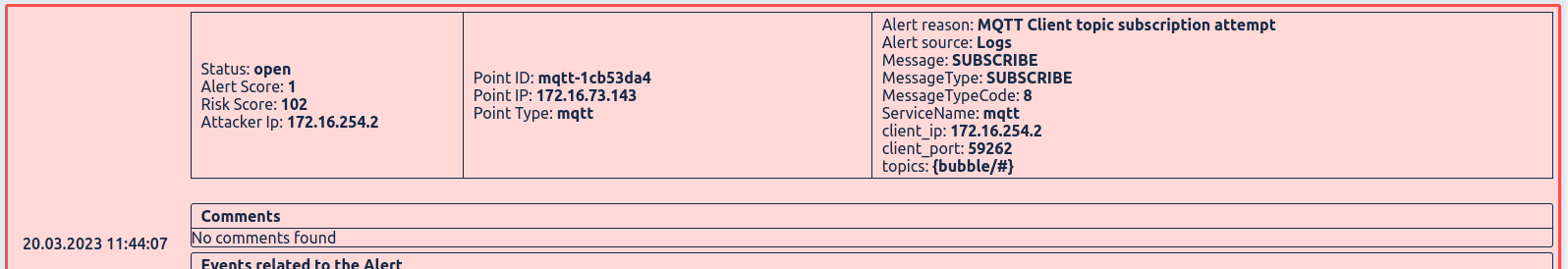
Currently, there are two options for implementing this type of Point:
- MQTT Broker with anonymous access to it. This means that when connecting to it, publishing notifications, or subscribing to topics, there is no need to authenticate.
- MQTT Broker with Authentication is a variant of the Point type that requires the client to authenticate with a username and a password corresponding to it.
1.4. User password reset
If the system user has lost or forgotten his password, the tenant administrator or superuser can reset it. In this case, a one-time password (OTP) will be generated, and the user must change the password to a new one at the next login.
1.5. Timezone awareness
Date, time, and time intervals are displayed to the user according to the time zone settings in the system. This includes the alert time on Point, the date range for dashboard data, the time range in Settings -> General -> Trusted IPs etc.
1.5. Improvement of the Latest Alerts sidebar
The new design of the sidebar makes it easier, faster, and better to analyze events.

1.6. KVM official support
Installation of an AdminVM on KVM-based platforms (Proxmox, OpenStack, etc.) is officially supported. Details of the installation process are described in the User Manual.
2. FIXES
2.1. The removal of the Seeder Agent with a large number of Seeder Tasks
In lab conditions, we noticed a problem with the removal of the Seeder Agent when a large number of Labyrinth regenerations were performed. It is currently fixed, but the team is ready to respond quickly in case of a recurrence.
Learn more about Labyrinth Deception Platform
iIT Distribution is the official distributor of Labyrinth. We offer an initial examination and assessment of your company's information security, selection of hardware and software, as well as full support during the implementation of selected cybersecurity solutions.
Back